This past weekend saw a flurry of Twitter-circulated rumors about a “raid” in Germany that supposedly recovered a server used by election software firm Scytl, a Spanish company that was bought out from bankruptcy in October 2020 by the Ireland-based Paragon Group.
Scytl, through its U.S. subsidiary in Florida, has provided product support to U.S. elections for a number of years. The original story was that U.S. voting information was being forwarded to the server in Europe for tabulation, and a U.S. team of some kind (variously described as a U.S. Army team and one composed of other government agents) seized the server in Germany shortly before the first report, which appears to have been on 8 November.
It isn’t the purpose of this article to adjudicate that reporting further. AP and Reuters have both reported that Scytl and the Army deny any such event. Scytl says it doesn’t have a server in Germany.
Rather, the incident serves as an informative introduction to the DHS agency known as CISA, or Cyber and Infrastructure Security Agency. After the Twitter rumors had bombed around for a couple of days, doing their best roller-derby imitation, the CISA director, Christopher Krebs, emerged with a tweet of his own, announcing that “election-related servers were NOT recently seized in Europe by the US Army contrary to #disinfo rapidly spreading across social media. Don’t buy it & think 2x before you share.”
Quick Election Security Disinfo Debunker: election-related servers WERE NOT recently seized in Europe by the US Army contrary to #disinfo rapidly spreading across social media. Don’t buy it & think 2x before you share. #Protect2020 https://t.co/qfwP6CypXX pic.twitter.com/ikjU1Sls0t
— Chris Krebs #Protect2020 (@CISAKrebs) November 15, 2020
Fine by me, since I had no investment in the story (and was already 100% sure the U.S. Army was not used for a raid of any kind whatsoever in Germany – where, if we had executed such an operation, it would probably have involved the FBI, in cooperation with the law enforcement agencies of a longstanding ally with which we have numerous cooperation and info-sharing agreements).
But there was something off about the tweet from Krebs. It was this: the tweet appended as its evidence a “fact-check” story by AP on the claimed incident.
That didn’t sound quite right. As between the Associated Press and a government agency with security oversight for “critical” U.S. election infrastructure, I’d rather hear from the U.S. agency, without any implication that the assurances of a news syndicate are needed to bolster the agency’s statement. The agency should have its own information on the matter.
AP should cite CISA, not the other way around.
What’s up with CISA?
Out of curiosity, I verified whether CISA, a DHS agency, has a 24-hour watch that would presumably be advised of something like election infrastructure being seized overseas – or would, because of being in that loop, be aware under its own charter that no such seizure had taken place. It would at the very least have the means to call the Army command in Europe (or U.S. European Command), the FBI, the DOJ, etc., and verify directly what the ground truth was.
There does seem to be such a watch, in the National Infrastructure Security Division. The National Infrastructure Coordinating Center seems to fill the relevant role.
Indeed, the NICC should also have Scytl on speed-dial, as an “owner … with significant business or operating interests in U.S. election infrastructure systems or services,” and a member of the Election Infrastructure Subsector Coordinating Council (EISCC).
According to the EISCC charter:
The EISCC will serve as the principal asset owner interface with other private critical infrastructure sectors as well as with the Department of Homeland Security (DHS), the U.S. Election Assistance Commission (EAC), the state, local and tribal governments (SLTTs), and the Election Infrastructure Subsector Government Coordinating Council (GCC).
Scytl, along with other voting systems about which significant questions have been raised, was an organizing member of the EISCC and as such is supposed to be partnered closely with DHS and CISA.

It seemed a bit odd – kind of freewheeling, if you will – that the CISA director would put out his assurance about the server story as a tweet citing a news source. If assurances from the agency were considered appropriate, a press statement by CISA, based on its own official information, would seem to be more in line with typical federal agency practice.
Shortly after Mr. Krebs sent his tweet, he was fired. It turned out that he was fired because his agency, CISA, issued another round of assurances related to the election through that more-typical channel; i.e., a formal press statement from the agency.
In that case, CISA exceeded its mandate by “releasing a joint statement made by multiple election agencies saying the presidential election was the ‘most secure in American history.’”
You needed to know what the EISCC is because it’s the first group listed in the CISA press release from 12 November, which claimed (bold in original): “The November 3rd election was the most secure in American history. …
“There is no evidence that any voting system deleted or lost votes, changed votes, or was in any way compromised.”
It’s not CISA’s job to certify that. Julio Rosas at Townhall: “This was wrong for Krebs to do, according to a DHS official, because addressing allegations of voter fraud from within the United States is not in CISA’s jurisdiction.”
Rosas goes on to quote the DHS official: “CISA was successful in preventing election interference via a cyberattack on election infrastructure during the presidential election. Election fraud is different than election interference and is beyond the scope of CISA authorities … CISA does not have firsthand information on allegations of voting fraud or investigate such claims, responsibility for which lies with State and local authorities and the Department of Justice.”
That would be two instances of CISA under Krebs issuing statements to the public that were apparently not based on firsthand information. One statement would conceivably have been in CISA’s lane to know the particulars on and to speak about to the public (the one about the alleged server seizure, which clearly has to do with infrastructure, per se). But it was not represented to be made with firsthand knowledge.
The other statement was not for CISA to make, but CISA made it anyway – and it was a heroically sweeping statement clearly out of kilter with the apparent evidence of discrepancies and irregularities in the 3 November vote. In its turn, it was (non-)based on firsthand knowledge CISA couldn’t have had, because on 12 November 2020, no one had it. In fact, it’s still to be determined in a number of jurisdictions.
The question arises: What kind of show are they running at CISA?
The things CISA was doing
It would take an extremely deep dive to unravel what’s been going on at CISA since it was stood up in 2018 as the successor to the National Protection and Programs Directorate (NPPD), the entity that previously held its portfolio within DHS.
But a number of things look “off” from out here, such as the point that all those commercial vendors whose systems have come under serious question in the last two weeks are “organizing members” of the EISCC, with the implication, at least, that they run tame at CISA. These are the selfsame vendors about which members of Congress and state election officials have been advancing significant complaints for more than a decade. What, exactly, has CISA been doing about those complaints? What did NPPD do?
U.S. election infrastructure was made a “critical” subsector of the national infrastructure monitored by DHS in January 2017, two weeks before Obama left office. It was something Jeh Johnson had been pushing since at least the summer of 2016, as a means of securing the nation’s election infrastructure against interference.
There’s far too much to try to lay out in one focused post on that. Most people would probably agree that whatever CISA has been doing about the Election Infrastructure Subsector, the effort hasn’t been attended by notable success.
You can get a flavor of the resource materials CISA assembled to support the 2020 election here; they seem to be mostly a collation of boilerplate about what the states do to secure and process the vote, and how to be an informed voter.
There’s nothing wrong with that, although it seems to largely overlap the offerings of the Election Assistance Commission (EAC), which was chartered by the Help America Vote Act (HAVA) of 2002.
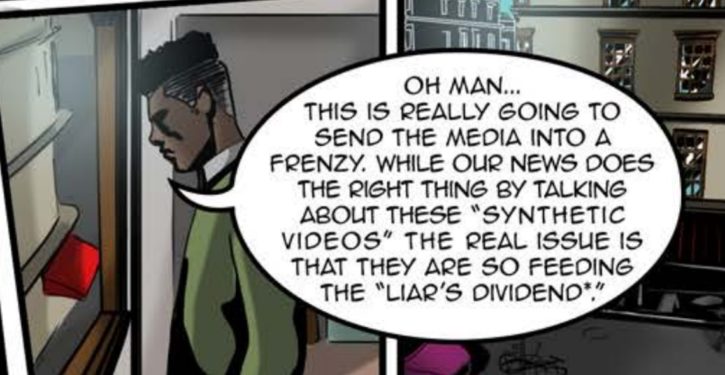
But alongside the presence of boilerplate and the rather glaring absence of any apparent effort to address the complaints about voting system vulnerabilities made repeatedly by U.S. officials, there is this peculiar specimen of election security information: a graphic novel depicting the hazards of Russian disinformation disseminated online by Russian-contracted trolls.
Real Fake
The novel, entitled Real Fake, walks us through an information battle against trolls retailing “deep fake” videos to spread disinformation before an election. (Clearly the U.S. election, as the senior wise-sensei person hovering over the effort is in New York, and an enterprising troll farm wants trolls proficient in American English.) At the outset, we get a load of an info warrior, Rachel, whose passion is democracy, getting into it via text message with a troll who talks about the “Deep State.”

The troll deals in deep fake videos, grrr, grrr. There’s an interlude explaining deep fakes, in which Richard Nixon and a conspiracy theory that we never really went to the moon make an appearance.
But it’s today’s voters who need to beware, as trolls are trying to get our democracies all up and sideways with their deep fakes. The action then shifts to … (you guessed it).
Some stuff happens in West Africa.
Our protagonist joins forces with a like-minded info-warrior.
Watch for the guy with the weird haircut, who seems to be a dupe, apparently being induced to invest in the troll factory on false premises and thereby fund election-meddling and democracy-threatening with deep-faked disinformation. There’s at least a happy ending, with a raided cesspit of disinfo-spinning and a lot of police tape.
The theme of the graphic novel reminded me forcibly of the intel skirmishes throughout 2020, in which the Democrats in Congress, and an intelligence official at DHS, were trying to force the national intelligence community to retail a specific propaganda theme that Russian meddling this year was all about planting evil stories against Joe Biden, by ordering Ukraine to investigate the Biden family activities there. DNI John Ratcliffe kept heading them off at the pass on that.
The DHS intel official involved was ultimately moved to another job, to the chagrin of the media who were obviously receiving a “leaked,” minute-by-minute account of these maneuvers.
In CISA, at the same time, our tax dollars were at work hammering the Russian-troll disinfo theme – apparently as an election security issue – on a more generic and artistically significant note.
Coda: Exemption from transparency
We may find it difficult to get to the bottom of all that’s been going on at CISA, however. The sector and subsector coordinating councils for national infrastructure security get a special exemption from the transparency required for such entities under U.S. law by the Federal Advisory Committee Act of 1972.

This exemption is provided in the charter of the Critical Infrastructure Partnership Advisory Council (CIPAC), of which all the sector and subsector coordinating councils, including EISCC, are members. (The link above is to an archive of the 2016 charter referenced in the EAC resource depicted below. The updated 2018 charter is here, with the same language.)
The purpose of the exemption is to allow “the critical infrastructure community to discuss vulnerabilities and problems without publically [sic] exposing potentially sensitive information.”
As the helpful EAC guide indicates, “For those participating in election sector coordinating councils this protection means that some information communicated between DHS and the coordinating councils can be protected. This limits the potential for sensitive election security information to be made public and protects potentially sensitive material from being misconstrued or used for nefarious purposes.”
We certainly wouldn’t want sensitive material about our voting systems to be misconstrued.









